Why Have Cyberattacks Increased in 2026?
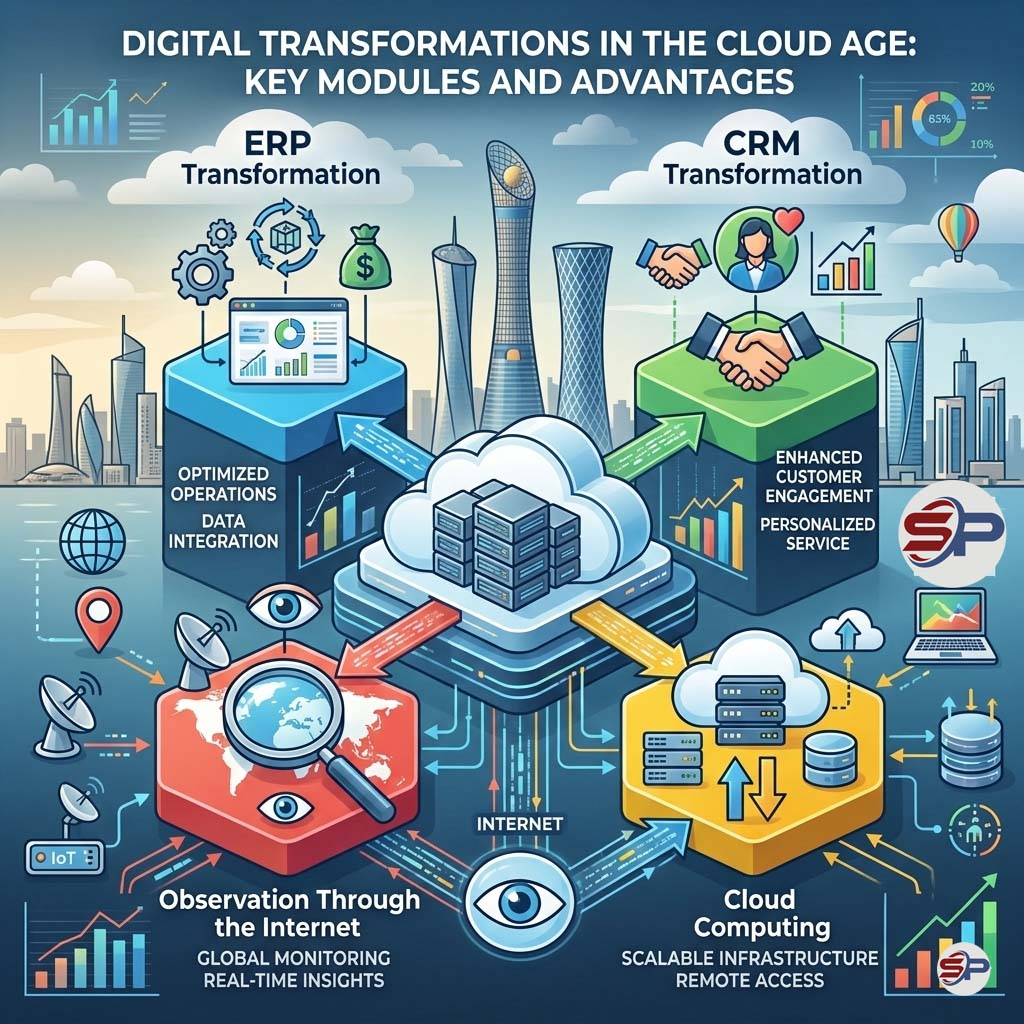
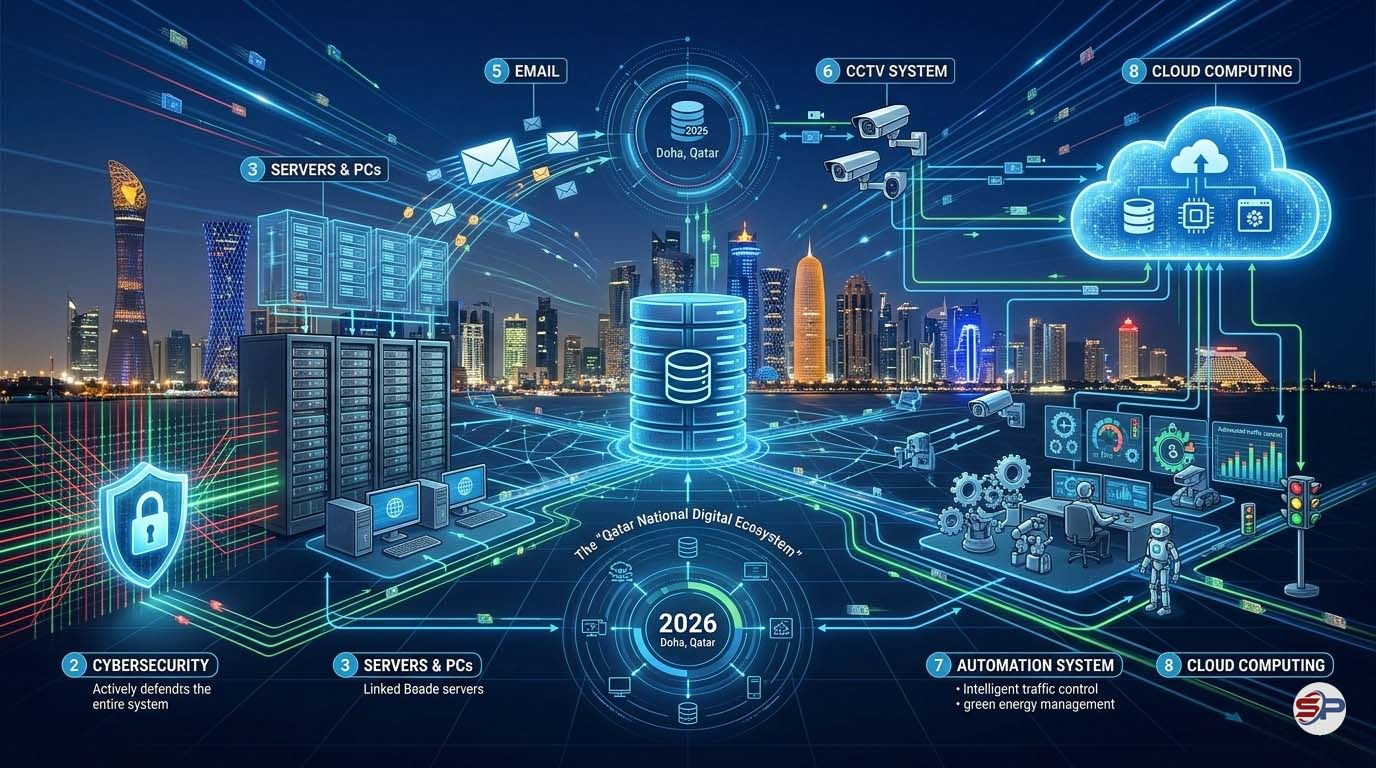
1️⃣ Full Digital Transformation
Companies now rely heavily on:
2️⃣ AI-Powered Hacking
Today, attackers use AI-based tools to detect vulnerabilities and launch automated attacks within minutes.
This means traditional security systems are no longer sufficient without:
The Most Dangerous Types of Cyberattacks on Businesses
Companies today face increasing cybersecurity threats that directly impact their data, reputation, and business continuity.
Among the most serious threats are Ransomware attacks, which encrypt a company’s data and demand payment in exchange for restoring access.
Phishing attacks are also among the most widespread cyber threats, where attackers deceive employees into revealing passwords or sensitive information through fraudulent emails or fake websites.
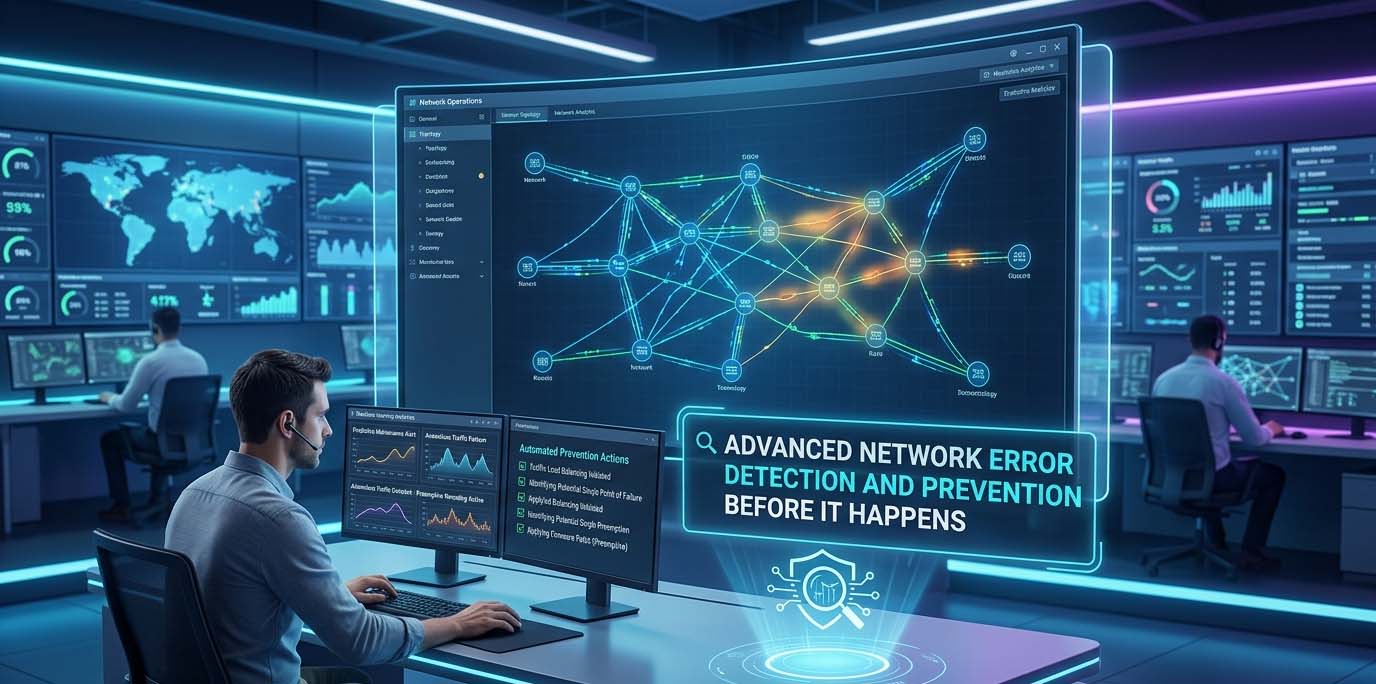
In addition, internal network breaches pose a major risk when attackers exploit system vulnerabilities to gain unauthorized access to company information and disrupt business operations.
🔴 Ransomware Attacks
Company data is encrypted, and a ransom is demanded for decryption.
Therefore, it has become necessary to take proactive steps to enhance cybersecurity and protect important data from loss or breach.

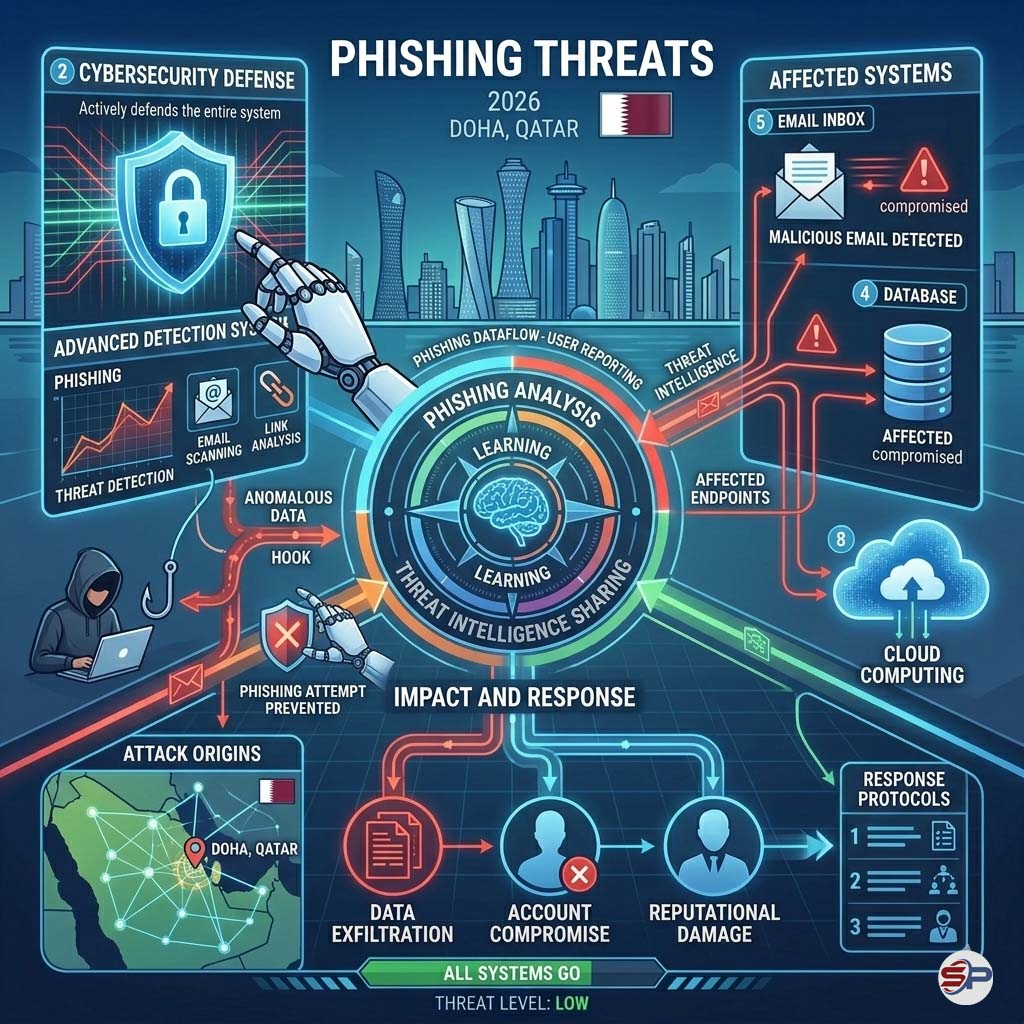
🔴 Phishing Attacks
Fake emails designed to steal:
Over 80% of cyberattacks begin with an email.
🔴 Internal Network Breaches
Weak configurations in:
can allow attackers easy access to servers.

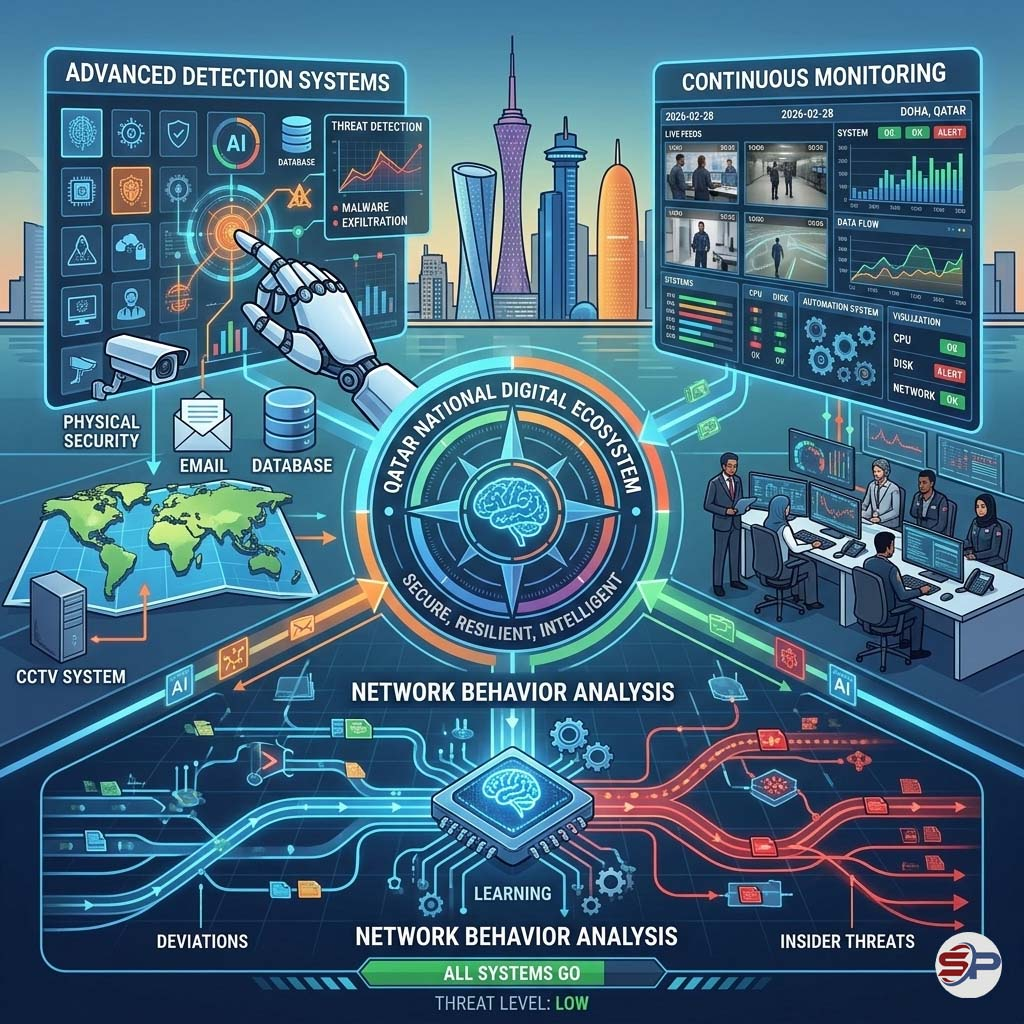
Best Cybersecurity Solutions for Businesses in 2026
With the rapid evolution of cyber threats, relying on a single security solution is no longer enough to protect modern businesses.
A successful cybersecurity strategy depends on a comprehensive security framework that combines advanced technology, strict security policies, and continuous employee training.
Implementing a Zero Trust security model, using a professional firewall, and properly segmenting networks significantly reduce the risk of cyber intrusions and limit the spread of internal threats.
In addition, having a daily backup strategy and 24/7 continuous monitoring ensures faster incident response and minimizes potential losses in the event of a cyberattack.
Regular system and software updates are equally critical, as most cyber breaches exploit outdated vulnerabilities that have not been patched.
Ultimately, investing in cybersecurity today is a direct investment in a company’s stability, reputation, and long-term business continuity.
|
💾 Backup Strategy Maintaining off-site or Cloud backups ensure rapid data recovery. |
🅾️ Implementing the Zero Trust Model
Trust no device or user without continuous verification. |
|---|---|
| 🛡️ (Next-Gen Firewall)
Provides: 1– Smart traffic filtering 2– Intrusion prevention 3– Application monitoring 4– Advanced detection |
🗓️ Regular System Updates
Includes: 1– Firmware 2– Windows / Linux and servers 3– Network device updates |
| 🛜 Network Segmentation
Separate: 1– Camera network 2– Employee network 3– Guest network 4– Servers This limits the spread of internal attacks. |
📺 Continuous Monitoring 24/7
Using systems such as: 1– IDS / IPS devices 2– SIEM 3– Endpoint devices to monitor network activity in real time. |
Cybersecurity 2026: Risks, Indicators, and Solutions
 Unexplained network slowdown, repeated login attempts, suspicious messages requesting password updates, surveillance system outages, and unusual server activity are all potential warning signs of a
Unexplained network slowdown, repeated login attempts, suspicious messages requesting password updates, surveillance system outages, and unusual server activity are all potential warning signs of a
 A professional security assessment helps with: Identifying security vulnerabilities, Analyzing network risks, Securing surveillance systems (CCTV), and Strengthening firewall configurations. Improving password security policies, Protecting sensitive business data 🔐
A professional security assessment helps with: Identifying security vulnerabilities, Analyzing network risks, Securing surveillance systems (CCTV), and Strengthening firewall configurations. Improving password security policies, Protecting sensitive business data 🔐
Nulla quis lorem ut libero malesuada feugiat. Vestibulum ac diam sit amet quam vehicula elementum sed sit amet dui. Vivamus suscipit tortor eget felis porttitor volutpat.

Cybersecurity is no longer just a technical option — it is a fundamental pillar of business continuity.
Whether you run a small business or a large enterprise, protecting your networks and surveillance systems from cyberattacks is a necessity that cannot be ignored.
By 2026, cyber threats have become more sophisticated, often powered by artificial intelligence and the exploitation of vulnerabilities in network-connected devices. Even a small security gap can turn into a serious breach that may cost you your data, reputation, and customer trust.
Proactive cybersecurity protection today can prevent major losses tomorrow.
Network Security + CCTV Security + Continuous Monitoring = A Secure Digital Environment. 🔐
Related Articles